Key Points
At Intruder, we are beating the drum about attack surface management and prioritization. So when our VP of Product, Andy Hornehold, joined a group of security and risk leaders at VISIONS + IMPACT Summit this week, he shared his insights on why not focusing on the vulnerabilities that pose a direct business impact will leave your attack surface exposed and derail your cyber security program.
Read the full article for a summary of the key points. And, if you’d like to hear Andy’s insights first-hand, register for our upcoming webinar or speak to us about signing up to Intruder today.
Stop trying to do everything, so you can finally get round to what counts
Before we dive into exposure management, I have a newfound hobby to share that, believe it or not, has significantly influenced my approach to cybersecurity - meditation. Thanks to an app called Waking Up (and a particularly revelatory book titled "Time Management for Mortals" by Oliver Burkeman), I've gained fresh perspectives on the importance of focusing on what truly matters. And, wouldn’t you know, that concept is surprisingly similar to what exposure management attempts to solve. I’ll explain...
Attack surface management vs exposure management
Attack surface management (ASM) is the ongoing process of discovering and identifying assets which can be seen by an attacker on the internet, showing where security gaps exist, where they can be used to perform an attack, and where defenses are strong enough to repel an attack. If there's something on the internet that can be exploited by an attacker, it typically falls under the realm of attack surface management. You can find out more in our essential guide to attack surface management.
Exposure management takes this a step further to include data assets, user identities, and cloud account configuration. It can be summarized as the set of processes that allow organizations to continually and consistently evaluate the visibility, accessibility, and vulnerability of their digital assets.
The continuous journey of managing threats
Continuous management is key for a number of reasons. Your business, your attack surface and the threat landscape are not static, they are constantly changing and evolving. New vulnerabilities are disclosed hourly, new exploits for old vulnerabilities are publicly released, and threat actors are updating their techniques continuously. Additionally, new systems and services are often exposed to the internet, and if you are running CI/CD processes, your applications are frequently updated, which could create exploitable security gaps.
Moving beyond CVEs
More and more, vulnerability management is being seen through a narrow lens of vulnerabilities that have CVEs. At Intruder we disagree with this approach, we believe that if there is a weakness in your attack surface it is a vulnerability regardless of whether it has a CVE associated or not.
So, unlike the narrow approach to vulnerability management, exposure management takes in the entire vista - including misconfigurations and potential weaknesses that don’t have an associated CVE. Take SQL injection, for example. It doesn’t have a CVE but it’s still a vulnerability in your application that could lead to serious consequences if exploited. Additionally, having Windows Remote Desktop exposed to the internet doesn’t have an associated CVE, but it introduces risk that an attacker can attempt to exploit. Ultimately, exposure management provides a common name for how we perceive and manage these threats.
.png)
.png)
.png)
Prioritizing vulnerabilities: the need for context
Currently, most vulnerability scanners provide a list of vulnerabilities, each as a standalone data point. For example, they might report: 'System X has vulnerability Y; you should go fix it.' However, when dealing with large numbers of vulnerabilities, this information alone isn't enough.
Effective prioritization requires more context to ensure that your team’s limited resource is focused on issues that will truly make a difference. For instance, it's crucial to understand which assets support your critical business functions, which vulnerabilities can be chained together to impact critical business functions, and where an attacker could potentially enter your network if these assets were exploited.
This approach transforms the management of vulnerabilities from siloed and isolated tasks into a cohesive strategy, providing the context needed to determine not only if a vulnerability should be fixed, but also when.
Much like meditation helps filter out the daily bombardment of thoughts and distractions, Intruder’s approach to exposure management aims to sift through the noise to focus on the issues that matter most.
Why exposure management matters
Exposure management matters because not everything that can be fixed, should be fixed immediately. Without a strategic approach, you risk wasting valuable time resolving low-impact issues, like an untrusted TLS certificate on an internal network, rather than addressing vulnerabilities that could lead to the compromise of a mission-critical system.
It is possible for you and your team to make a disproportionate and even more meaningful impact on your organization’s risk profile by having more time to focus on strategically important activities that secure your organization more effectively. This can be achieved by avoiding a knee-jerk reaction to each vulnerability (akin to playing whack-a-mole), which is what exposure management aims to achieve.
It is possible to reduce the volume of tasks that your team are carrying out by scoping out your environment, understanding which assets support business critical processes, establishing dedicated teams responsible for the remediation of those assets, and setting thresholds or triggers that specify when issues need to be addressed.
The need for exposure management
Recent examples of attackers gaining total control through seemingly innocuous entry points are aplenty.
A developer at Microsoft discovered a deliberately placed backdoor in xz-utils, an essential data compression utility for Linux and Unix-like operating systems. This vulnerability, found in versions 5.6.0 and 5.6.1, allowed an unknown threat actor to execute commands on systems which were running these versions of xz-utils and had SSH exposed to the internet. The discovery's timing was incredibly lucky, it was discovered before the compromised versions of xz-utils could make it into many mainstream Linux distributions like Debian and Red Hat.
Although there were no reported cases of exploitation, the potential risks were substantial. A threat actor would have gained access to those systems, giving them a jumping off point to compromise other systems on any connected network to extract any and all sensitive data.
Security teams will have spent time and effort chasing down whether they were exposed. With exposure management, it would have been easy to identify any affected versions within your environments and quickly establish that the exposure was minimal since the compromised versions of xz-utils aren’t that widespread.
Interestingly, the effort to embed the backdoor took four years, revealing a calculated and long-term scheme to compromise open-source software. This isn’t necessarily new, but it shines a spotlight on the fact that advanced persistent threats aren’t just focused on large enterprises; if threat actors can compromise an open source package like xz-utils and have it reach mainstream distributions, then everyone is at risk.
Then there’s Palo Alto Networks. It issued an urgent call for companies to patch a critical zero-day vulnerability, known as CVE-2024-3400, in its widely used PAN-OS software that powers GlobalProtect firewall products. This flaw, found in the newer versions of the software, allows attackers to take complete control of an affected firewall remotely without requiring authentication, thus representing a significant threat to thousands of businesses relying on these firewalls for security. Given its potential for straightforward remote exploitation, Palo Alto has given this vulnerability the highest severity rating. Using attack surface management tools available to you, identifying vulnerable assets should be nearly instantaneous, and with an exposure management process in place the threshold for remediation should have allowed those responsible for remediation or mitigation to kick into action quickly.
These examples demonstrate how threats can be effectively shutdown if organizations shift from a reactive, rush-to-fix approach to proactive exposure management, where they continuously manage their attack surface.
Starting your journey towards effective exposure management
Getting started with exposure management starts with practical, manageable steps:
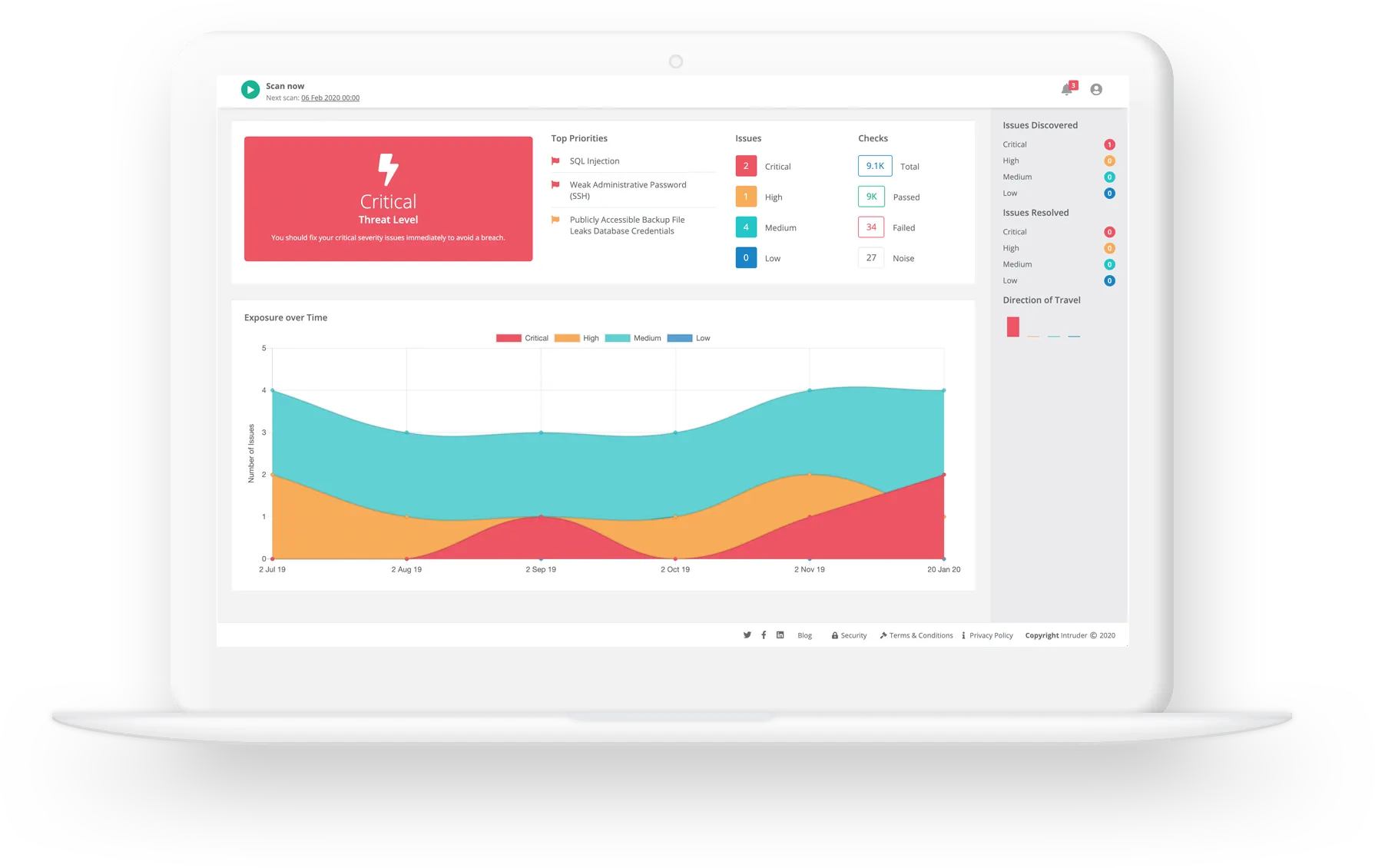
- Use what you already have: First, remember you can leverage the services you’re already using. For example, if you're using a tool like Intruder, you already have a vulnerability management and attack surface management provider that can kick-start your approach to exposure management. Alternatively, a consultancy service can conduct attack path mapping exercises and threat profile workshops.
- Define your scope: When defining the scope of what your exposure management process will cover, focus first on assets that are exposed to the internet, as these are often most vulnerable to attack. Intruder can help by providing you with a view of your internet-facing systems, which you can use as a starting point for your exposure management process. You can also use Intruder’s target tagging to segment systems into your defined scopes. In the scoping process, you’re also looking to identify individuals who are responsible for remediating the risk when a vulnerability is detected; you can add those users to Intruder and empower them to fix and validate that any issues have been resolved. If the data is available, also remember to keep track of the SaaS applications you use, as they can contain sensitive data and credentials.
- Discover and prioritize your assets: Use a tool to identify known and unknown assets and identify which are business-critical and support the scope you’ve defined previously. If you’re using Intruder then we’re already helping you cover this step, Intruder automatically discovers new cloud assets by integrating with your cloud accounts. Soon, you’ll also be able to discover other assets that aren’t in your cloud accounts but which contribute to your attack surface. You can also add context to your assets by using tags to specify how systems contribute to your business processes, and what risk they pose to those processes if they were compromised.
- Carry out weakness discovery and prioritization: The focus next shifts to assessing which of these assets are most at risk of being compromised and which would be the most attractive targets for cyber attackers. With Intruder you can find vulnerabilities in your infrastructure, applications, and APIs, and receive a prioritized list of issues so you know what to act on first. We also provide a continuous approach to vulnerability discovery and prioritization by monitoring your network, showing you what’s exposed and kicking off scans when anything changes.
- Act: Then it's time to act, be that through remediation, mitigation, or risk acceptance. Intruder makes it easy to manage and verify your remediation efforts. Run remediation scans, export issues to your ticketing systems, set up alerts in Slack and Teams, and more.
Intruder helps give you time back to focus on what matters most
One of our customers shared how Intruder gives them back time, which is exactly what we are here to do.

Bringing it all back home
Ultimately, we all have a limited amount of time.
By minimizing distractions and enabling your team to focus on what truly matters, exposure management allows you to achieve the greatest impact with the least time invested.
If your team is focusing on the 25% of vulnerabilities that actually matter, they have 75% extra time to focus on the activities that are critical to keeping your business secure.
Intruder aims to equip organizations to focus on the significant, the impactful, and ultimately, secure their digital landscape in today’s fast-paced world.
And if that means more peaceful weekends for our customers (and myself), confidently stepping away from our desks knowing our assets are protected, then I believe we are on the right path. Perhaps, it's not so much about managing vulnerabilities or exposures but about managing our focus in the endless stream of cybersecurity threats.
Want a deeper dive into exposure management and your attack surface? Register for our upcoming webinar or get in touch with us for a demo to see it in action today.